Shutting Down GSG Project-Specific Mailing Lists
Thank you to everyone who has been a part of the GSG project mailing lists. We at Great Scott Gadgets appreciate all of the conversations and friendships that have been forged on these lists. Over the last few years we have not given our project-specific mailing lists the attention they deserve; instead we have been focusing our efforts on Discord and GitHub. As such, we will be disabling all the mailing lists except for GSG-announce. Links to the mailing list archives for Ubertooth, YARD Stick One, GreatFET One, and HackRF will all remain available on their individual product pages. Current links to the archives are here:
ANT700 Release
Today we are excited to announce the official release of ANT700, our new 300—1100 MHz telescopic antenna. Because this general purpose antenna was designed with YARD Stick One users in mind, it has a slim and lightweight form factor that works well with smaller devices. It has an SMA male connector to attach to your device of choice (including HackRF One) and can be extended from 9.5 cm to 24.5 cm.
We started distributing ANT700 last month, and it is already available for purchase from six of our authorized resellers on four continents. To find out where you can purchase yours, please visit the product page.

Low Cost SimpliSafe Attacks
Earlier this week, Dr. Andrew Zonenberg of IOActive published a security advisory and blog post describing weaknesses in the SimpliSafe home security system. He showed that components of the system, such as the keypad, transmit unencrypted radio signals that can be captured and replayed. He also pointed out the significant problem that SimpliSafe devices are physically incapable of being reprogrammed with improved firmware that might address such vulnerabilities.
I know Andrew and have great respect for his reverse engineering and hardware hacking talents. He implemented a replay attack by making small modifications to SimpliSafe devices, monitoring and controlling them from his own hardware platform. To demonstrate the impact of the technique, he showed how it could be used to replay a PIN that disarms a SimpliSafe system. While I found his attack very effective, I was intrigued by his inability to fully decode PINs. I wanted to take a crack at the problem myself, and I thought it would be worthwhile to confirm that the radio interface of the system can be attacked at a lower cost to the attacker, without any SimpliSafe hardware, and without physical proximity to the target system.
I borrowed a SimpliSafe system to use as a target system, and I took the approach I have demonstrated in my presentation, Rapid Radio Reversing, using a combination of Software Defined Radio (SDR) and non-SDR tools. The primary tool I used was YARD Stick One with RfCat software.
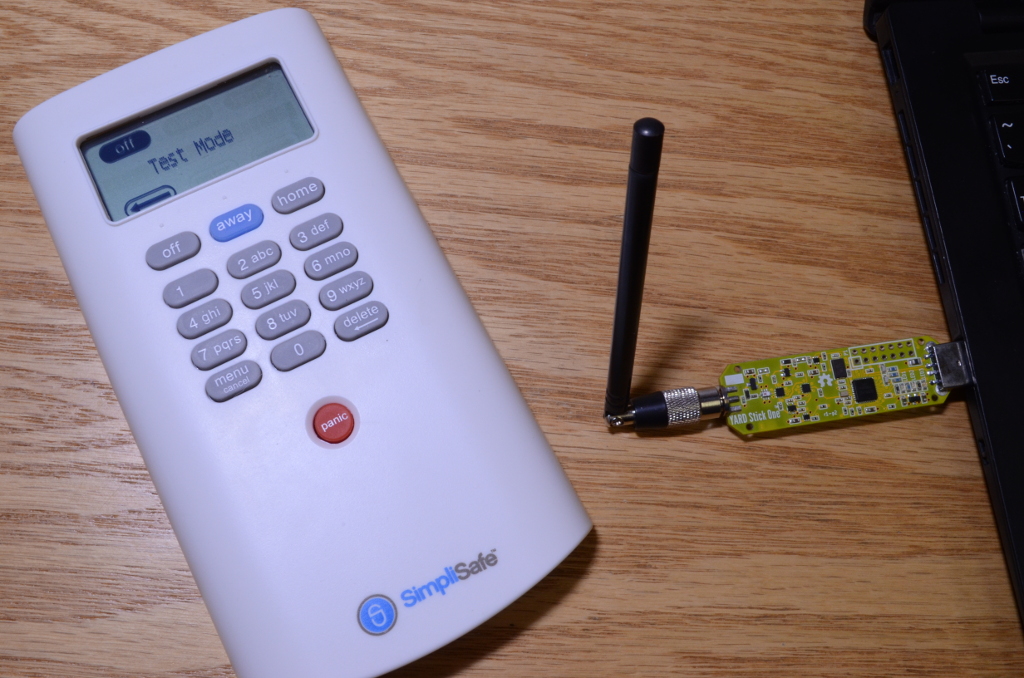
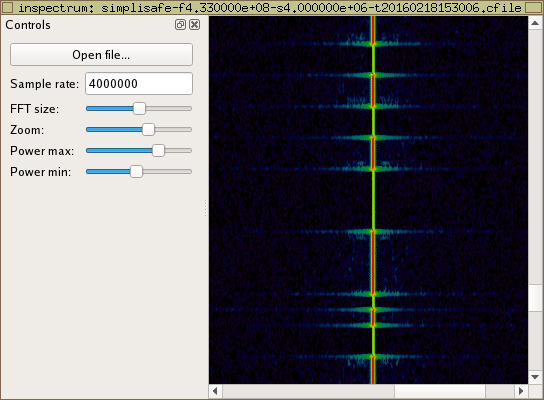
First I used HackRF One to monitor transmissions from the SimpliSafe keypad. I visualized a captured radio waveform with inspectrum and quickly identified an Amplitude Shift Keying (ASK) signal being transmitted by keypad. Andrew labeled this On-Off Keying (OOK), but the difference between ASK and OOK is subtle and does not affect his findings.
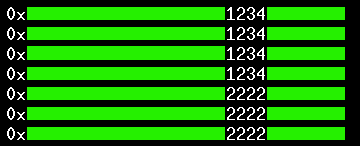
After determining the frequency, modulation, and symbol rate of the transmission, I turned to YARD Stick One for further analysis. Within seconds I was able to decode raw symbols being transmitted by the keypad. It was easy to identify which packets were transmitted by the keypad after entering a PIN, so I entered a few different PINs and saved the resulting packets for analysis.
It took me a couple hours of staring at packets and fiddling with short decoding functions in Python before I was able to understand the encoding. This was the most difficult part of the project. The system uses a somewhat uncommon Pulse Interval and Width Modulation (PIWM) to encode data onto the ASK signal, and the order of bits was not immediately obvious. With a little time, however, I was able to implement real-time decoding of received packets and to recover the PIN entered on the keypad by another person at a distance. I was also able to replay keypad transmissions.
I could have implemented capture and replay even without fully decoding the packets. This is what Andrew was able to accomplish with his hardware hack. Full decoding, however, demonstrates that some additional attacks are possible. An attacker with a good antenna can monitor PINs from a great distance and can, without ever transmitting a radio signal, learn those PINs and later use them at the keypads. An attacker can craft packets with chosen PINs or other contents, so an automated brute force attack on a PIN is possible even if the attacker has not observed the valid PIN. The system uses 4-digit pins, so only 10,000 guesses are required for an exhaustive brute force attack.
I could have accomplished all of this with only HackRF One or only YARD Stick One, but I used the combination of the two for convenience. If I had to choose just one for a project like this, it would be YARD Stick One which, at $100, costs less than half of the equipment used by Andrew. It could be done with almost any 433 MHz ASK transceiver, including the covert TURNIPSCHOOL or my favorite children's toy, the IM-Me, but YARD Stick One with RfCat is the most convenient tool for the job in my toolbox.
Andrew included with his blog post a video demonstrating his attack over-the-air. In his video, he mentions that his hardware hack was the "quickest and easiest way" to accomplish his attack. That may be true for Andrew, but personally I found it easier to use radio tools. I wrote dozens of lines of Python compared to his hundreds of lines of C, and I never needed to crack open any SimpliSafe device. It took me about half a day, and most of that time was spent puzzling over the data encoding. I could have implemented a simple capture and replay within seconds of identifying the radio signal.
Andrew's video shows him disarming an alarm from only a few inches away which unfortunately could be interpreted as meaning that his attack is only effective at such close range. His attack, in fact, works from anywhere the keypad can operate. According to the manual, it works within 100 feet of the base station. Even greater range can be achieved easily with the use of low cost radio test tools instead of a modified keypad. I estimate that, for less than the $250 Andrew spent, an attacker can execute PIN replay from about a mile away.
Since Andrew's advisory, SimpliSafe has responded in predictable fashion while information security professionals filled their bingo cards. One of the things SimpliSafe has pointed out is that customers are notified whenever their systems are disarmed. Unfortunately this is only true for those customers who pay an extra $10 per month for SMS and email notifications. Moreover, in my testing, I verified that it is possible for an attacker to wirelessly command the SimpliSafe system to enter test mode even while the system is armed. This is something that normally can be done from the SimpliSafe keypad only while the system is disarmed. Alarms and notifications are disabled in test mode, but the documentation states that test mode is indicated in the online dashboard available to customers who pay for notifications.
Following Andrew's lead, I am not publishing any attack software developed during my testing. However, it is important to realize that I employed only tools and techniques that are well known and commonly used throughout the wireless security community. Effective attacks, including PIN replay, can be implemented without writing a single line of code. Passive monitoring attacks, such as the ability to learn a PIN at a distance, require somewhat more reverse engineering effort but can be implemented with even less expensive equipment such as off-the-shelf TV tuners that cost as little as $10.
Andrew's and my investigations only scratch the surface of the security of the SimpliSafe system. Andrew's key finding is not that PINs can be replayed but that the absence of basic cryptographic protections illustrates a total lack of wireless security engineering. Further weaknesses will very likely be discovered if anyone takes the time to look for them. For example, the cellular interface is an attack vector that remains unexplored as far as I know.
SimpliSafe is not alone in deploying alarm systems with vulnerable wireless interfaces. Sadly, almost every wireless alarm system I've ever looked at suffers from similar weaknesses. As we hurtle toward a future of ubiquitous digital wireless technology embedded in the objects of our daily lives, we would be wise to pay more attention to the security of those wireless interfaces. Burglar alarm systems seem like a good place to start.
P.S. Dr. Zonenberg's dissertation is fascinating.
Rapid Radio Reversing, ToorCon 2015
In this video of Michael Ossmann’s presentation at ToorCon 2015, he demonstrates how helpful it can be to use a combination of both SDR and non-SDR tools for reverse engineering wireless systems. Michael uses both HackRF One and YARD Stick One to reverse engineer a wireless cabinet lock.
You can download and watch the video on Internet Archive here.
The code from the presentation is in Michael Ossmann’s stealthlock repository.
Introducing YARD Stick One
This week we started shipping YARD Stick One, our latest test tool for radio systems operating below 1 GHz. The first thing you should know about it is that, unlike our popular HackRF One, YARD Stick One is not a Software Defined Radio (SDR) platform. Although we think that SDR is the overall best tool for the greatest number of wireless applications, sometimes it is beneficial to have a simpler tool for certain jobs.
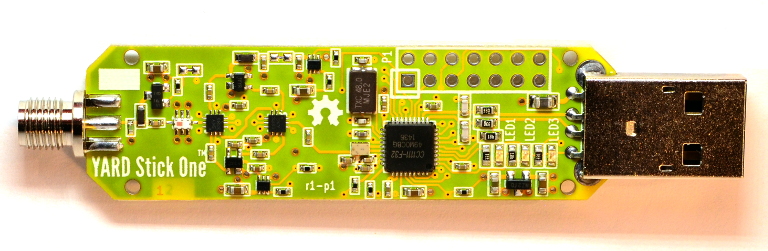
The architecture of YARD Stick One is similar to Ubertooth One; it is a wireless transceiver IC on a USB dongle. The IC takes care of digital modulation and demodulation, giving you an easy-to-use interface for your own software running on the attached host computer. YARD Stick One is the quickest and easiest way to start experimenting with low speed digital wireless technologies including industrial control systems, wireless sensor networks, smart meters, home automation systems, garage door openers, and remote keyless entry systems.
The YARD Stick One story started when Travis Goodspeed introduced me to the IM-Me one snowy night at ShmooCon in 2010. He showed me how to use his GoodFET to program firmware on the IM-Me, and we successfully tested radio transmission from the IM-Me in the hotel bar. After returning home, I acquired an IM-Me, soldered up the GoodFET Travis had given me (which was the first surface mount PCB I ever assembled), and immediately set to work developing a spectrum analyzer application which, to this day, remains perhaps the most useful software available for the popular, hackable toy.
Months later, Travis and I presented Real Men Carry Pink Pagers in which we encouraged others to use the CC1110-based platform for testing and experimenting with digital radio communication systems. About a year after that, atlas started showing people how to use the CC1111, the USB-enabled version of the CC1110, to accomplish the same things with a dongle connected to a laptop. His RfCat software allowed people to do things in a few lines of Python that Travis and I achieved only by compiling C for the 8051 microcontroller inside the CC11xx.
RfCat made experimentation with low speed digital wireless systems easier than ever before, but it wasn't adopted as widely as I hoped it would be. Probably the biggest reason for that is the fact that, for a long time, the only way to get RfCat up and running was to buy a CC1111 development board, assemble a GoodFET yourself, and then use the GoodFET to write RfCat firmware onto the CC1111 board. It became apparent early on that we needed a device designed specifically for RfCat, one that ships with RfCat firmware and is ready to use. I designed the ToorCon 14 badge, which was a great success, but I wanted to make an even better platform available to the world.
YARD Stick One was intended to be the ideal platform for RfCat. In addition to shipping with RfCat firmware, YARD Stick One is designed to operate effectively over the entire frequency range of the CC1111. All of the previous CC1111 boards that I know of are designed to work in only one frequency band. For example, you can get a CC1111 development board for 900 MHz or one for 433 MHz, but, prior to YARD Stick One, you couldn't find a CC1111 board that worked well in both those bands.
Where previous development boards have had built-in antennas, YARD Stick One has an SMA connector that allows the use of higher performance external antennas. It also has receive and transmit amplifiers for improved RF performance. Like everything we make, YARD Stick One is open source hardware.
It took a long while to complete YARD Stick One and get it manufactured, but we are finally shipping. Over the past couple years I've been able to get pre-release boards out to atlas and a few other folks who are active in wireless security research. For example, Samy Kamkar used YARD Stick One for the remote keyless entry system research that he presented at DEF CON in August.
To get started with YARD Stick One, I recommend atlas's videos along with several blog posts written by early adopters of RfCat. You'll notice that, even though the users of RfCat tend to be well versed in SDR, they find RfCat useful to get hacking even faster on digital wireless communication systems.
